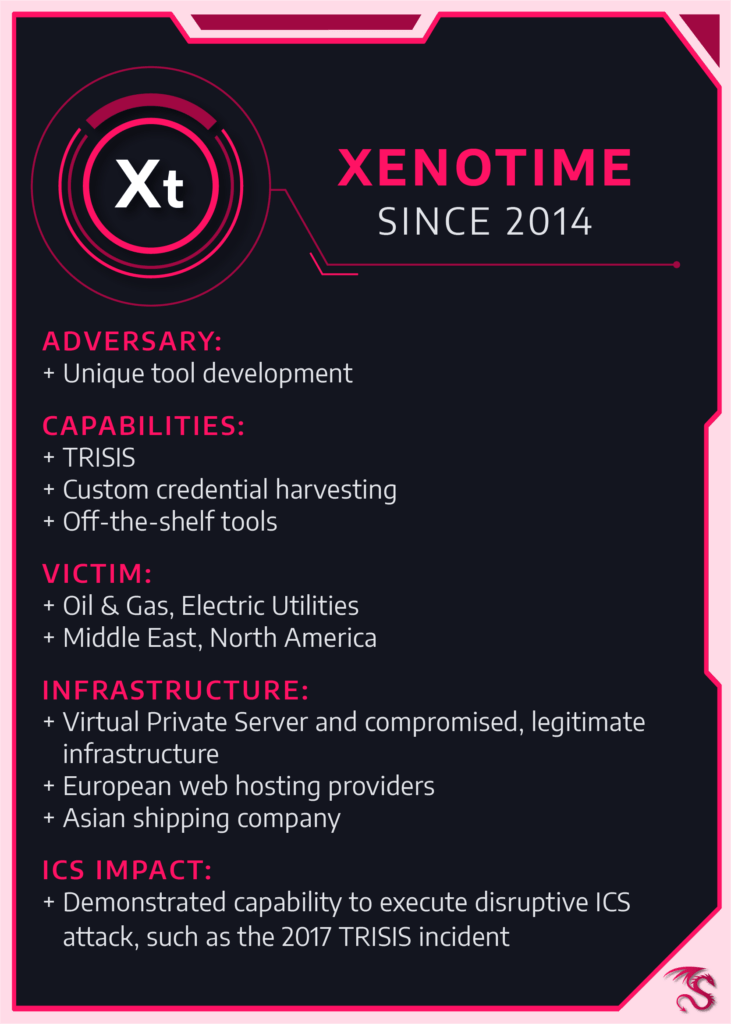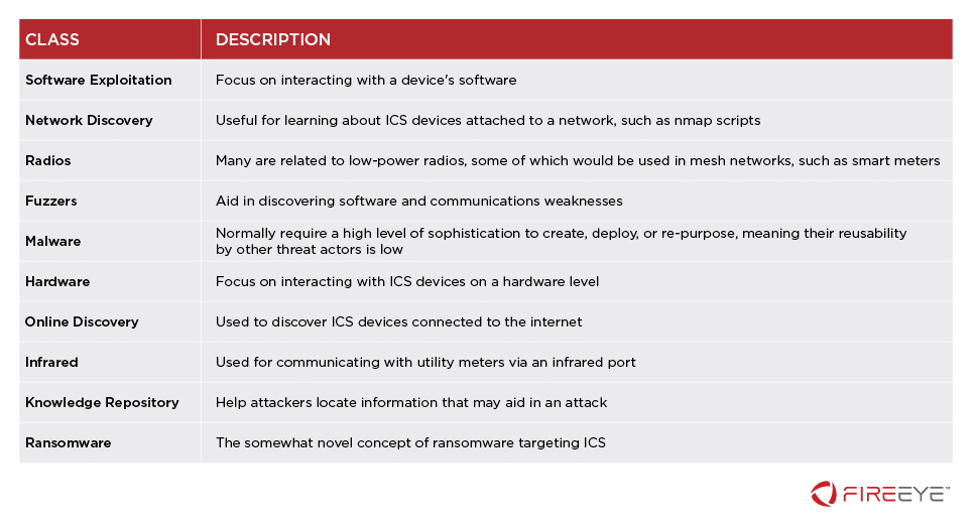
Monitoring ICS Cyber Operation Tools and Software Exploit Modules To Anticipate Future Threats | Mandiant
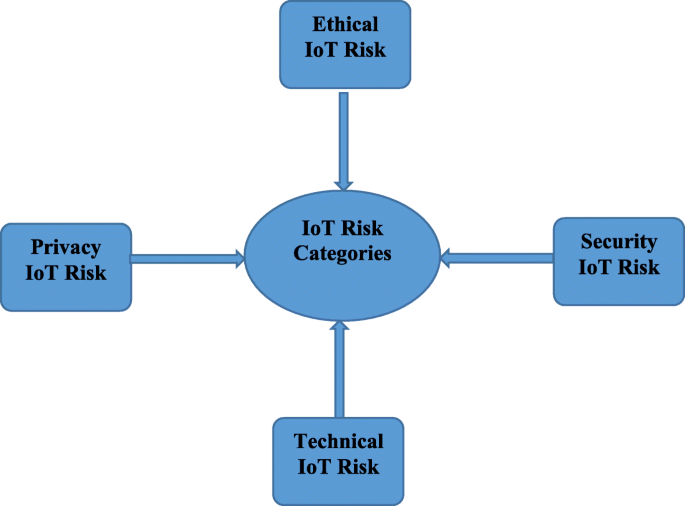
IoT cyber risk: a holistic analysis of cyber risk assessment frameworks, risk vectors, and risk ranking process | EURASIP Journal on Information Security | Full Text

NIST Cybersecurity Framework is Good and Bad, Experts Say ~ DigitalCrazyTown | Cybersecurity framework, Cyber security, Business analysis